Why choose Panoptica?
Four reasons you need the industry’s leading cloud-native security solution.
These Cisco Terms of Use (this “Agreement”) between You and Cisco cover Your use of the Software and Cloud Services (“Cisco Technology”) obtained through this site. The Cisco Technology is intended for use by business users. Definitions of capitalized terms are in Section 11. You agree to be bound by the terms of this Agreement through (a) Your download, installation, or use of the Cisco Technology; or (b) Your express agreement to this Agreement. If You do not have authority to enter into this Agreement or You do not agree with its terms, do not use the Cisco Technology.
2.1 License and Right to Use. Cisco grants You, for Your direct benefit during the Usage Term and for the full scope of Your Entitlement under this Agreement, a non-exclusive, non-transferable (except with respect to Software as permitted under the Cisco Software Transfer and Re-Use Policy) (a) license to use the Software; and (b) right to use the Cloud Services (collectively, the “Usage Rights”).
2.2 Use by Third Parties. You may permit Authorized Third Parties to exercise the Usage Rights on Your behalf, provided that You are responsible for (a) ensuring that such Authorized Third Parties comply with this Agreement; and (b) any breach of this Agreement by such Authorized Third Parties.
2.3 Free Service. Cisco is making this Cisco Technology available to You without charge, up to certain capacity limits as described in Section 10 below, and subject to the terms of this Agreement. You agree that Cisco, in its sole discretion and for any or no reason, may terminate Your Usage Rights (or any part thereof) and that any termination may be without prior notice and without liability to Cisco. Cisco may, for example, suspend or terminate Your Usage Rights if (i) Cisco has reason to believe that You engaged in any fraudulent behaviour as it relates to the Cloud Services, or (ii) You use Cisco Technology beyond Your Entitlement. You are solely responsible for exporting Your customer data from the Cisco Technology prior to termination, and, except as required by law, Cisco will provide You a reasonable opportunity to retrieve such data.
2.4 Upgrades or Additional Copies of Software. You may only use Upgrades or additional copies of the Software beyond Your Entitlement if You have (a) acquired those rights under a support agreement covering the applicable Software; or (b) You have purchased the right to use Upgrades or additional copies separately.
2.5 Interoperability of Software. If required by law and upon Your request, Cisco will provide You with the information needed to achieve interoperability between the Software and another independently created program, provided You agree to any additional terms reasonably required by Cisco. You will treat such information as Confidential Information.
3.1 Cisco Technology Generally. Unless expressly agreed by Cisco, You may not (a) transfer, sell, sublicense, monetize, or make the functionality of any Cisco Technology available to any third party; (b) use the Software on second hand or refurbished Cisco equipment not authorized by Cisco, or use Software that is licensed for a specific device on a different device (except as permitted under Cisco’s Software License Portability Policy); (c) remove, modify, or conceal any product identification, copyright, proprietary, intellectual property notices or other marks; (d) reverse engineer, decompile, decrypt, disassemble, modify, or make derivative works of the Cisco Technology; or (e) use Cisco Content other than as part of Your permitted use of the Cisco Technology. 3.2 Cloud Services. You will not intentionally (a) interfere with other users’ access to, or use of, the Cloud Service, or with its security; (b) facilitate the attack or disruption of the Cloud Service, including a denial of service attack, unauthorized access, penetration testing, crawling, or distribution of malware (including viruses, trojan horses, worms, time bombs, spyware, adware, and cancelbots); (c) cause an unusual spike or increase in Your use of the Cloud Service that negatively impacts the Cloud Service’s operation; or (d) submit any information that is not contemplated in the applicable Documentation. 3.3 Evolving Cisco Technology. Cisco may: (a) enhance or modify the features, functionality, and capacity limits of this Cisco Technology at any time, in its sole discretion, without liability; and (b) perform scheduled maintenance of the infrastructure and software used to provide the Cloud Service, during which time You may experience some disruption to that Cloud Service. Whenever reasonably practicable, Cisco will provide You with advance notice of such maintenance. You acknowledge that, from time to time, Cisco may need to perform emergency maintenance without providing You advance notice, during which time Cisco may temporarily suspend Your access to, and use of, the Cloud Service.
Cisco reserves the right (a) to end the life of this Cisco Technology, including component functionality, (“EOL”), and/or (b) to incorporate all or some of the features and functionality of this Cisco Technology into a Cisco paid offer at any time, in its sole discretion, and without liability (“Cisco Offering”). Any new Cisco Offering will be subject to its own terms and conditions.
3.4 Protecting Account Access. You will keep all account information up to date, use reasonable means to protect Your account information, passwords and other login credentials, and promptly notify Cisco of any known or suspected unauthorized use of or access to Your account. 3.5 Use with Third-Party Products. If You use the Cisco Technology together with third-party products, such use is at Your risk. You are responsible for complying with any third-party provider terms, including its privacy policy. Cisco does not provide support or guarantee ongoing integration support for products that are not a native part of the Cisco Technology. 3.6 Open Source Software. Open source software not owned by Cisco is subject to separate license terms as set out at www.cisco.com/go/opensource. The applicable open source software licences will not materially or adversely affect Your ability to exercise Usage Rights in applicable Cisco Technology.
4.1 Confidentiality. Recipient will hold in confidence and use no less than reasonable care to avoid disclosure of any Confidential Information to any third party, except for its employees, affiliates, and contractors who have a need to know (“Permitted Recipients”). Recipient: (a) must ensure that its Permitted Recipients are subject to written confidentiality obligations no less restrictive than the Recipient’s obligations under this Agreement, and (b) is liable for any breach of this Section by its Permitted Recipients. Such nondisclosure obligations will not apply to information that: (i) is known by Recipient without confidentiality obligations; (ii) is or has become public knowledge through no fault of Recipient; or (iii) is independently developed by Recipient. Recipient may disclose Discloser’s Confidential Information if required under a regulation, law or court order provided that Recipient provides prior notice to Discloser (to the extent legally permissible) and reasonably cooperates, at Discloser’s expense, regarding protective actions pursued by Discloser. Upon the reasonable request of Discloser, Recipient will either return, delete or destroy all Confidential Information of Discloser and certify the same. 4.2 How We Use Data. Cisco will access, process and use data in connection with Your use of the Cisco Technology in accordance with applicable privacy and data protection laws. For further detail, please visit Cisco’s Security and Trust Center. 4.3 Notice and Consent. To the extent Your use of the Cisco Technology requires it, You are responsible for providing notice to, and obtaining consents from, individuals regarding the collection, processing, transfer and storage of their data through Your use of the Cisco Technology.
Except where agreed in writing, nothing in this Agreement transfers ownership in, or grants any license to, any intellectual property rights. You retain any ownership of Your content and Cisco retains ownership of the Cisco Technology and Cisco Content. You acknowledge and agree that any questions, comments, suggestions, ideas, feedback or other information about this Cisco Technology provided by You to Cisco (“Feedback”) are non-confidential and Cisco may use any Feedback You provide in connection with Your use of the Cisco Technology as part of its business operations without acknowledgment or compensation to You.
To the extent allowed by applicable law, Cisco expressly disclaims all warranties and conditions of any kind, express or implied, including without limitation any warranty, condition or other implied term as to merchantability, fitness for a particular purpose or non-infringement, or that the Cisco Technology will be secure, uninterrupted or error free. If You are a consumer, You may have legal rights in Your country of residence that prohibit the limitations set out in this Section from applying to You, and, where prohibited, they will not apply
Neither party will be liable for indirect, incidental, exemplary, special, or consequential damages; loss or corruption of data or interruption or loss of business; or loss of revenues, profits, goodwill, or anticipated sales or savings. The maximum aggregate liability of each party under this Agreement is limited to $5,000 USD. These limitations of liability do NOT apply to liability arising from (a) Your breach of Sections 2.1 (License and Right to Use), 3.1 (Cisco Technology Generally), 3.2 (Cloud Services) or 9.7 (Export). These limitations of liability apply whether the claims are in warranty, contract, tort (including negligence), infringement, or otherwise, even if either party has been advised of the possibility of such damages. Nothing in this Agreement limits or excludes any liability that cannot be limited or excluded under applicable law. These limitations of liability are cumulative and not per incident.
8.1 Suspension. Cisco may immediately suspend Your Usage Rights if You breach Sections 2.1 (License and Right to Use), 3.1 (Cisco Technology Generally), 3.2 (Cloud Services) or 9.7 (Export). 8.2 Termination. Cisco, in its sole discretion and for any or no reason, may terminate Your access to this Cisco Technology or any part thereof and any termination may be without prior notice and without liability to Cisco. Cisco may, for example, suspend or terminate Your access immediately if You breach Sections 2.1 (License and Right to Use), 3.1 (Cisco Technology Generally), 3.2 (Cloud Services), or 9.7 (Export). Upon termination of this Agreement, You must stop using the Cisco Technology and destroy any copies of Software and Confidential Information within Your control.
9.1 Survival. Sections 4 (Confidential Information and Use of Data), 5 (Ownership), 7 (Liability), 8 (Termination and Suspension), and 9 (General Provisions) survive termination or expiration of this Agreement. 9.2 Third-Party Beneficiaries. This Agreement does not grant any right or cause of action to any third party. 9.3 Assignment and Subcontracting. Except as set out below, neither party may assign or novate this Agreement in whole or in part without the other party’s express written consent. Cisco may (a) by written notice to You, assign or novate this Agreement in whole or in part to an Affiliate of Cisco, or otherwise as part of a sale or transfer of any part of its business; or (b) subcontract any performance associated with the Cisco Technology to third parties, provided that such subcontract does not relieve Cisco of any of its obligations under this Agreement. 9.4 U.S. Government End Users. The Software, Cloud Services and Documentation are deemed to be “commercial computer software” and “commercial computer software documentation” pursuant to FAR 12.212 and DFARS 227.7202. All U.S. Government end users acquire the Cisco Technology and Documentation with only those rights set forth in this Agreement. Any provisions that are inconsistent with federal procurement regulations are not enforceable against the U.S. Government 9.5 Modifications to this Agreement. Cisco may change this Agreement or any of its components by updating it on Cisco.com and/or the Documentation page, which can be found at https://community.cisco.com/. Cisco will exercise commercially reasonable efforts to provide notice of any material changes to this Agreement, and within three (3) business days of posting changes to this Agreement, they will be binding. If you do not agree with the changes, you must discontinue using the Cisco Technology at that time. If you continue using the Cisco Technology after that time, you will be deemed to have accepted the changes to this Agreement. 9.6 Compliance with Laws. Each party will comply with all laws and regulations applicable to their respective obligations under this Agreement. Cisco may restrict the availability of the Cisco Technology in any particular location or modify or discontinue features to comply with applicable laws and regulations.
If You use the Cisco Technology in a location with local laws requiring a designated entity to be responsible for collection of data about individual end users and transfer of data outside of that jurisdiction (e.g., Russia and China), You acknowledge that You are the entity responsible for complying with such laws.
9.7 Export. Cisco’s Software, Cloud Services, products, technology, and services (collectively the “Cisco Products”) are subject to U.S. and local export control and sanctions laws. You acknowledge and agree to the applicability of and Your compliance with those laws, and You will not receive, use, transfer, export, or re-export any Cisco Products in a way that would cause Cisco to violate those laws. You also agree to obtain any required licenses or authorizations 9.8 Governing Law and Venue. This Agreement, and any disputes arising from it, will be governed exclusively by the applicable governing law below, based on Your primary place of business (or primary residence, if you are not a business) and without regard to conflicts of laws rules or the United Nations Convention on the International Sale of Goods. The courts located in the applicable venue below will have exclusive jurisdiction to adjudicate any dispute arising out of or relating to the Agreement or its formation, interpretation or enforcement. Each party hereby consents and submits to the exclusive jurisdiction of such courts. Regardless of the below governing law, either party may seek interim injunctive relief in any court of appropriate jurisdiction with respect to any alleged breach of Cisco’s intellectual property or proprietary rights
Your Primary Place of Business Governing Law Jurisdiction and Venue Any location not specified below
| State of California, United States of America | Superior Court of California, County of Santa Clara and Federal Courts of the Northern District of California | Australia | Laws of the State of New South Wales, Australia | State and Federal Courts of New South Wales | | Canada | Province of Ontario, Canada | Courts of the Province of Ontario | | China | Laws of the People’s Republic of China | Hong Kong International Arbitration Center | | Europe (excluding Italy), Middle East, Africa, Asia (excluding Japan and China), Oceania (excluding Australia) | Laws of England | English Courts | | Italy | Laws of Italy | Court of Milan | | Japan | Laws of Japan | Tokyo District Court of Japan | | United States, Latin America or the Caribbean | State of California, United States of America | Superior Court of California, County of Santa Clara and Federal Courts of the Northern District of California |
If You are a United States public sector agency or government institution located in the United States, the laws of the primary jurisdiction in which You are located will govern this Agreement and any disputes arising from it. For U.S. Federal Government users, this Agreement will be controlled and construed under the laws of the United States of America. 9.9 Notice. Any notice delivered by Cisco to You under this Agreement will be delivered on Cisco.com. Notices to Cisco should be sent to Cisco Systems, Inc., Office of General Counsel, 170 West Tasman Drive, San Jose, CA 95134. 9.10 Force Majeure. Neither party will be responsible for failure to perform its obligations due to an event or circumstances beyond its reasonable control. 9.11 No Waiver. Failure by either party to enforce any right under this Agreement will not waive that right. 9.12 Severability. If any portion of this Agreement is not enforceable, it will not affect any other terms. 9.13 Entire agreement. This Agreement is the complete agreement between the parties with respect to the subject matter of this Agreement and supersedes all prior or contemporaneous communications, understandings or agreements (whether written or oral). 9.14 Translations. Cisco may provide local language translations of this Agreement in some locations. You agree that those translations are provided for informational purposes only and if there is any inconsistency, the English version of this Agreement will prevail. 9.15 Order of Precedence. If there is any conflict between this Agreement and any Cisco policies expressly referenced in this Agreement, the order of precedence is: (a) this Agreement; then (b) any applicable Cisco policy expressly referenced in this Agreement. 9.16 Language Election for Purchasers in Quebec. You confirm Your Agreement that this Cisco Technology is currently provided in English only.
10.1 Restrictions on Use by Minor Children. This Cisco Technology is not intended for use by persons younger than the age of consent in their relevant jurisdiction (e.g.,13 years old in the United States under the US Children’s Online Privacy Protection Act of 1998, or 16 or 13 years old in the European Union as per Member State law) (“Minor Children”). Minor Children are not permitted to create an account and You will not authorize Minor Children to access the Cisco Technology.
10.2 Capacity Restrictions. Your right to access and use this Cisco Technology is currently limited to five (5) nodes dedicated to applications/microservices.
10.3 Limited Community Support. This Cisco Technology is provided on a free-of-charge basis, as-is, and without support. Cisco has no obligation to maintain, repair, or upgrade this Cloud Service and Cisco will not provide user support services in connection with this Cisco Technology. User can refer to self-service help materials that cover a range of topics or reach out to our community forum to engage in community support discussions on our Documentation page at https://community.cisco.com/. Cisco makes no representations about and has no liability for these community support resources. All use of these resources, and the advice and guidance therein, is at Your own risk.
10.4 No Competitive Analysis. By agreeing to these terms, You represent and warrant that you will not use this Cisco Technology or its Documentation to (a) copy ideas, features, functions, or graphics; (b) develop competing products or services; or (c) perform competitive analyses.
10.5 Beta Functionality. User acknowledges and agrees that all or some components or functionality of the Cisco Technology may be in beta stage and may not have been (and may not become) productized or commercialized. You acknowledge that Your use and evaluation of this Cisco Technology is at Your own risk.
“Affiliate” means any corporation or company that directly or indirectly controls, or is controlled by, or is under common control with the relevant party, where “control” means to: (a) own more than 50% of the relevant party; or (b) be able to direct the affairs of the relevant party through any lawful means (e.g., a contract that allows control). “Authorized Third Parties” means Your Users, Your Affiliates, Your third-party service providers, and each of their respective Users, permitted to access and use the Cisco Technology on Your behalf as part of Your Entitlement. “Cisco” “we” “our” or “us” means Cisco Systems, Inc. or its applicable Affiliate(s). “Cisco Content” means any (a) content or data provided by Cisco to You as part of Your use of the Cisco Technology and (b) content or data that the Cisco Technology generates or derives in connection with Your use. Cisco Content includes geographic and domain information, rules, signatures, threat intelligence, and data feeds, and Cisco’s compilation of suspicious URLs. “Cloud Service” means the Cisco hosted software-as-a-service offering or other Cisco cloud-enabled feature described in this Agreement. Cloud Services include applicable Documentation and may also include Software. “Confidential Information” means non-public proprietary information of the disclosing party (“Discloser”) obtained by the receiving party (“Recipient”) in connection with this Agreement, which is (a) conspicuously marked as confidential or, if verbally disclosed, is summarized in writing to the Recipient within a reasonable time period after disclosure and marked as confidential; or (b) is information which by its nature should reasonably be considered confidential whether disclosed in writing or verbally. “Delivery Date” means the date on which the Cloud Service is made available for Your use or, when Usage Rights in Software and Cloud Services are granted together, the earlier of the date Software is made available for download, or the date on which the Cloud Service is made available for Your use. “Documentation” means the technical specifications and usage materials officially published by Cisco or available on https://community.cisco.com/ specifying the functionalities and capabilities of the applicable Cisco Technology. “Entitlement” means the specific metrics, duration, and quantity of Cisco Technology that You acquire from Cisco under this Agreement. “Software” means the Cisco computer programs including Upgrades, firmware and applicable Documentation. “Upgrades” means all updates, upgrades, bug fixes, error corrections, enhancements and other modifications to the Software. “Usage Term” means the period commencing on the Delivery Date and continuing until expiration or termination of the Entitlement, during which period You have the right to use the applicable Cisco Technology. “User” means the individuals (including contractors or employees) permitted to access and use the Cisco Technology on Your behalf as part of Your Entitlement. “You” means the individual or legal entity using the Cisco Technology.
NEW Cloud Security Academy Level up your skills with hands-on lessons. Get started
×Jump right in! Find out all about Panoptica and try it for yourself.
Secure your applications from development to runtime.
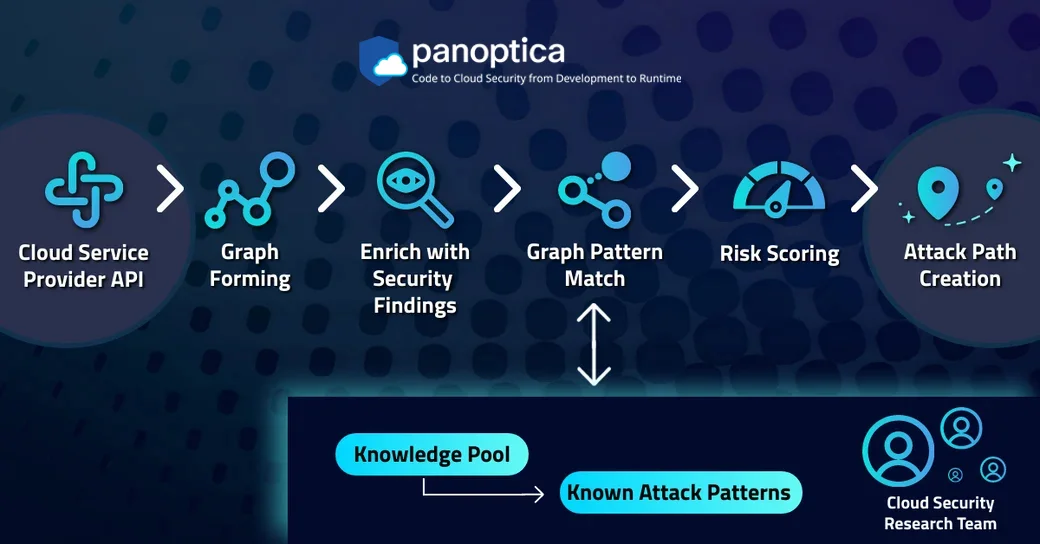
Attack-Path Analysis
Look at paths from diverse angles and get help with risk mitigation and resolution.
Cloud Native Application Security Solution
Reduce tools and vendors as you create secure, compliant cloud native apps.
Code & CI/CD Security
Get real-time vulnerability detection from development to runtime.
Data Security Posture Management (DSPM)
Classify and prioritize your data risks with greater precision aided by enhanced data discovery.
Smart Cloud Detection & Response (Smart CDR)
Real-time attack detection using AI/ML models trained for threat hunting.
Cloud Workload Protection (CWP)
Scale across environments and prioritize real-time risks for cloud workloads.
Cloud Security Posture Management (CSPM)
Scan, monitor, and remediate critical attack paths in your cloud stack instantly.
API Security
Inventory APIs, assess risk, and analyze specs with a single solution.
GenAI Solutions
Dive deeper into cloud risks with industry-leading context-aware GenAI for cloud native application security.
CIEM Solutions
Secure cloud identities by enforcing least-privilege access, reduce identity-based threats, and ensure compliance.
Integrations & Partners
Easily work from one platform with all the tools you already know and love using our integrations.
Get Started
Jump right in! Find out all about Panoptica and try it for yourself.
Solutions
Secure your applications from development to runtime.
Attack-Path Analysis
Look at paths from diverse angles and get help with risk mitigation and resolution.
Cloud Native Application Security Solution
Reduce tools and vendors as you create secure, compliant cloud native apps.
Code & CI/CD Security
Get real-time vulnerability detection from development to runtime.
Data Security Posture Management (DSPM)
Classify and prioritize your data risks with greater precision aided by enhanced data discovery.
Smart Cloud Detection & Response (Smart CDR)
Real-time attack detection using AI/ML models trained for threat hunting.
Cloud Workload Protection (CWP)
Scale across environments and prioritize real-time risks for cloud workloads.
Cloud Security Posture Management (CSPM)
Scan, monitor, and remediate critical attack paths in your cloud stack instantly.
API Security
Inventory APIs, assess risk, and analyze specs with a single solution.
GenAI Solutions
Dive deeper into cloud risks with industry-leading context-aware GenAI for cloud native application security.
CIEM Solutions
Secure cloud identities by enforcing least-privilege access, reduce identity-based threats, and ensure compliance.
Integrations & Partners
Easily work from one platform with all the tools you already know and love using our integrations.

Efficiently protecting the cloud at scale You probably know our amazing research team from the cloud vulnerabilities they’ve discovered such as the AWS RDS Vulnerability, the AWS ECR Public Vulnerability, or the Azure Cloud Shell Command Inj...


Digesting vast amounts of data stored on modern data platforms such as a graph database is a primary benefit of true cloud attack path analysis. This is called contextual cloud security at scale. And it’s the key to noise reduction, improvement in...

Cloud security is a giant field for good reason: 77% of CIOs say their IT environment changes once every minute or less. As you can imagine, the dynamic nature of cloud computing makes preventing, detecting and fixing vulnerabilities ...


The shift to cloud-native app development on Kubernetes is in full force. Today, cloud-native has become the strategy of choice in the software industry. There are plenty of reasons the industry is preferring cloud-native software development over l...

Understand why SBOMS are vital as part of covering your cloud estate and better securing your environments. What is an SBOM? SBOM or the Software Bill of Materials is the inventory package that comprises the different software components ...

Cloud security is broad and complex by nature – but it comes with a lot of specific terms and acronyms. That’s why we put together this continuously growing glossary of cloud security terms. Use this as a guide to help you unravel the nuance...

In an effort to support continuous development and release of new features at the lightning speed of today’s market, forward-looking organizations have been moving to cloud-native architectures in droves. The reasons are obvious: these decentraliz...
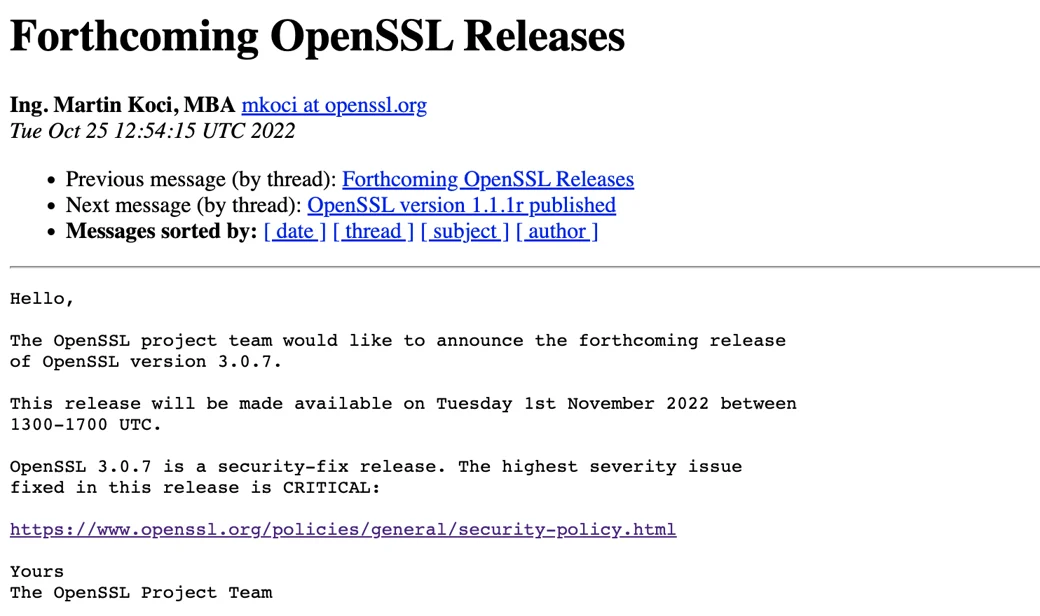

Tomorrow is “patch Tuesday” and it's a notable one. The OpenSSL project team announced last week that they will be releasing OpenSSL version 3.0.7, with a patch to fix a critical security vulnerability. Until the vulnerability details ...

Graph technology can help examine your data from a new perspective. Find out how graph technology may find previously unseen relationships in your data. What Is Graph Technology? Graph technology includes graph theory, graph analytics, and gra...

Agentless scanning is an important security tool. We discuss how it works, how it differs from agent-based scanning, and if your organization requires both. What is Agentless Scanning? Agentless scanning is a method of inspecting the vulnerabi...
© 2024 Cisco Systems, Inc.